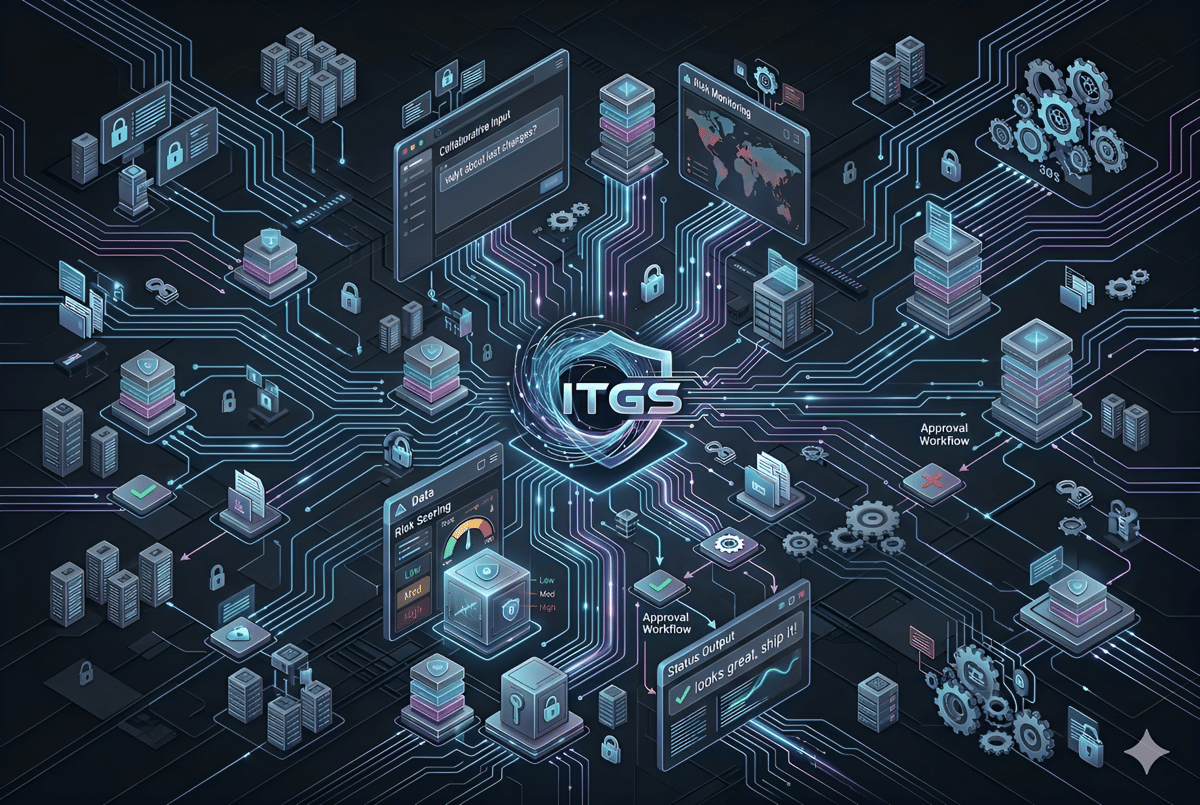
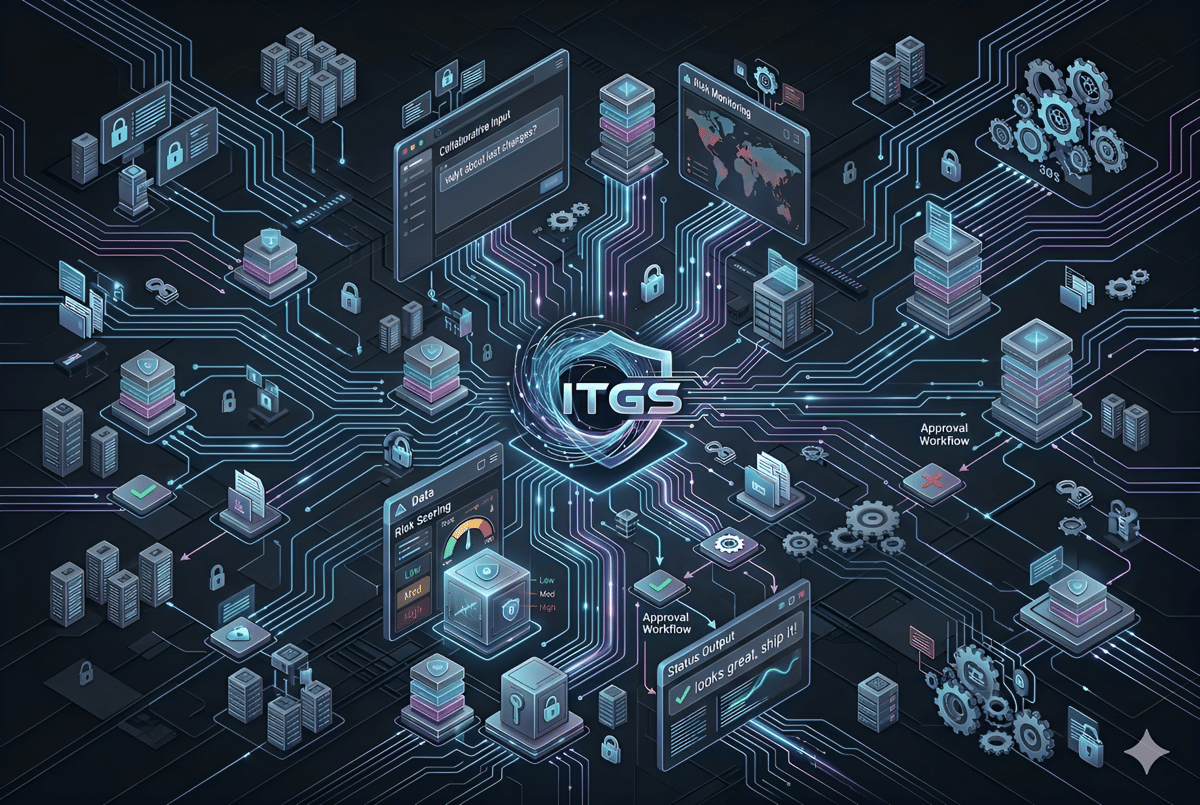
Continuous Vulnerability Scanning
Our platform performs 24/7 automated scans to detect security gaps across your entire infrastructure. This ensures threats are identified and prioritized before they can be exploited.
- Automated threat detection
- Real-time risk scoring (Low, Medium, High)
- Prioritized remediation alerts